
Guests
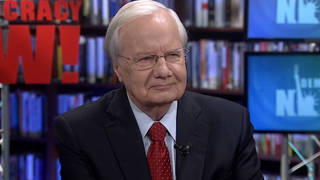
- William ArkinNBC news analyst who obtained the Pentagon documents exposing the database. He is a former military intelligence officer who has written several books, including Code Names: Deciphering U.S. Military Plans, Programs, and Operations in the 9/11 World. He also writes a blog on national and homeland security for The Washington Post called Early Warning.
Newly leaked Pentagon documents have confirmed the military has been monitoring and collecting intelligence on anti-war groups across the country. Peace protests are being described as threats and the military is collecting data on who is attending demonstrations. We speak with William Arkin, the former Army intelligence officer, who obtained the secret Pentagon documents. [includes rush transcript]
Earlier this week NBC News exposed the existence of a secret Pentagon database to track intelligence gathered inside the United States. The database including information on dozens of anti-war protests and rallies particularly actions targeting military recruiting.
The list included: counter-military recruiting meetings held at a Quaker Meeting House in Lake Forth, Florida. Anti-nuclear protests staged in Nebraska on the 50th anniversary of the U.S. atomic bombing of Nagasaki. An anti-war protest organized by military families outside Fort Bragg in North Carolina. And a rally in San Diego to support war resister Pablo Parades. The Pentagon database described all of these events as threats.
The documents obtained by NBC also indicate the Pentagon is now conducting surveillance at protests and possibly monitoring Internet traffic. One Pentagon briefing document stamped “secret” concluded: “[W]e have noted increased communication and encouragement between protest groups using the [I]nternet.” The same document indicated the military is tracking who is attending protests in part by keeping records on cars seen at protests.
The Washington Post is reporting today that the Pentagon has ordered a review of the military intelligence program following the NBC News report.
The Pentagon’s domestic intelligence gathering has been done through a secretive program called TALON which allows military bases and other defense installations to file reports of suspicious activity into a consolidated database.
The TALON program is so secret that even the number of reports in the database is classified. Also classified is the size and budget of the agency overseeing the database–the Counterintelligence Field Activity. The agency was created three years ago following the Sept. 11 attacks.
The Pentagon also now has a toll-free number for citizens to report suspicious activity directly to the military. The number of the hotline is 1-800-CALL-SPY.
- 1-800-CALL-SPY–recorded message.
Just Last week Richard Ben-Veniste of the Sept. 11 commission expressed concern that Congress has paid too little attention to the TALON program. He said “I am particularly apprehensive about the expansion of our military’s role in domestic intelligence gathering.”
- William Arkin, NBC news analyst who obtained the Pentagon documents exposing the database. He is a former military intelligence officer who has written several books including “Code Names: Deciphering U.S. Military Plans, Programs, and Operations in the 9/11 World.” He also writes a blog on National and Homeland Security for the Washington Post called Early Warning.
Transcript
AMY GOODMAN: The Pentagon also now has a toll-free number for citizens to report suspicious activity directly to the military. The number of the hotline is 1-800-CALL-SPY.
SPY HOTLINE: You have reached the U.S. Army Call Spy hotline. You may remain anonymous. Please leave a detailed message of the incident you wish to report. Your call is important. If you wish to be contacted, please leave your name and telephone number. If this is an emergency, please contact your local office of the F.B.I. Thank you.
AMY GOODMAN: Just last week, Richard Ben-Veniste of the September 11 Commission expressed concern that Congress has paid too little attention to the TALON program. He said, quote, “I’m particularly apprehensive about the expansion of our military’s role in domestic intelligence gathering.” In a few minutes, we’ll talk to several activists connected to events listed in the Pentagon database. But first, we turn to William Arkin. He’s the NBC news analyst who obtained the Pentagon documents exposing the database. William Arkin is a former military intelligence officer, who has written several books, including Code Names: Deciphering U.S. Military Plans, Programs and Operations in the 9/11 World. He also writes a blog on national and homeland security for the Washington Post called ” Early Warning.” Welcome to Democracy Now! again, William Arkin.
WILLIAM ARKIN: Thank you, Amy.
AMY GOODMAN: It’s good to have you with us. Why don’t you start by just laying out how you got these documents and what exactly they say?
WILLIAM ARKIN: Well, I got the documents from military sources. It is an actual database in an Excel spreadsheet, and it took some doing on my part to clean it up and eliminate the duplicate incidents and put it in a form that was useful to begin to understand what is it that we have here, because it’s by no means clear what it is that is here. However, it identifies specific incidents, all in the United States, as well as the source of those incidents, that is, the report issuer and the classification. And it’s in that actual data about the report issuer that one can see the degree of Pentagon monitoring in the United States of not just things that go on inside military bases, but also things that go on in our communities, from particularly suspicious incidents associated with military recruiting stations, which as you know are located all over the United States in malls and in shop fronts, in office buildings, and this is sort of the thin edge of understanding, and therefore, a smaller number of incidents that are associated with anti-war and anti-military protests or planned protests throughout the United States.
JUAN GONZALEZ: The information that you got, as I understand, only covers a period of about ten months, between July of 2004, May of 2005?
WILLIAM ARKIN: That’s correct.
JUAN GONZALEZ: So the 1,500 incidents would be about 150 a month on average that are being catalogued?
WILLIAM ARKIN: That’s correct. And again, as I wrote yesterday in my blog, you know, I wouldn’t want to leave the impression that what we’re seeing here is merely a devious and menacing activity of the U.S. military. What we’re also seeing here is just gross bureaucratic incompetence and overstatement.
Here’s how it works. The military has a mission of protecting Defense Department interests and installations. In the course of trying to figure out whether or not there is a threat or that there is some dots to be connected that would indicate a threat, they compile all of this information. Even though many of these reports are not credible or are resolved without any incident or without any threat determined, the accumulation and repetition of so many incidents, 150 a month, as you say, certainly suggests a greater threat and certainly suggests a threat. And so, therefore, it becomes a kind of self-perpetuating bureaucratic activity. Oh, my, we have 1,500 incidents in less than a year, certainly indicates that we better keep a close eye on all of this, even though when one goes into the database, the number of actual terrorist incidents which are found credible by the military itself is really only two dozen.
AMY GOODMAN: Welcome Arkin. Yesterday the House passed the USA PATRIOT Act, extended it. The Senate is going to debate it. Now, how does this relate to that? I mean, does the Pentagon fall under the USA PATRIOT Act?
WILLIAM ARKIN: It does, yes, and there are more strict rules for the military on collecting information on U.S. persons. There are much more stringent requirements, and those came out of 1960s and 1970s spying on the part of the Pentagon, so there were created rules that limited how much information they could collect, what type of information they could collect, and the provisions under which they had to pass that information on to law enforcement agencies when it was considered to be a valid issue of breaking the law.
But I think that the link between the TALON program of the counter intelligence field activity and other military domestic intelligence programs and the USA PATRIOT Act is the environment of threat which is suggested, that there is somehow a justification that our traditional civil liberties or the traditional role of the military, which I would argue is a foreign role, should somehow be revised to include domestic duties, is necessary, and that’s based upon a — I would argue — a false picture of the actual threat of terrorism in the United States, and certainly, a false picture that somehow anti-war or anti-military protesters in the United States constitute some sort of a link with transnational terrorist activity.
JUAN GONZALEZ: And in terms of the information that you gathered, was it strictly aimed at meetings and events, or were individuals tracked, as well, in these files?
WILLIAM ARKIN: The detail in the documents don’t really give us an answer to that question. We can see, for instance, in the case of the meeting which NBC highlighted in its show on Tuesday night, the Ft. Worth, Florida anti-military protesters at a Quaker meetinghouse, we can see that the incident occurred. We can see on the date, and clearly those activists, who I understand might be on your show today, are going — you know, we’re able to say, yes, we met on this date. It gives reference to a report, with a report number of the 902nd Military Intelligence Group, which is the Army’s military intelligence organization that is responsible for both counterterrorism, counter-intelligence and force protection in the United States. My guess would be that when we obtain that report, and eventually some patriot will either leak it to us or we’ll get it under the Freedom of Information Act, we’ll see that they did record the names of the people at meeting and that they did check those names against watch lists and databases and did their jobs, but I’m just — in the database itself, what we see is only a sliver of insight into what it is that the military is actually up to.
AMY GOODMAN: Bill Arkin, we’re going to break and then come back to this discussion, NBC analyst. He is the author of the book, Code Names, where he exposed names of many top secret government operations. When we come back, we are going to hear from activists that look like they have been targeted, from around the country, including Lake Worth, Florida.
[break]
AMY GOODMAN: As we talk to William Arkin, NBC news analyst, former army intelligence analyst, author of the book, Code Names: Deciphering U.S. Military Plans, Programs and Operations in the 9/11 World. Bill, I’m looking at a piece from the National Journal from a few weeks ago, and it says, “To help the government track suspected terrorists and spies who may be visiting or residing in the country, the F.B.I. and the Defense Department for the past three years have been paying a Georgia-based company for access to its vast databases that contain billions of personal records on about nearly every person, citizens and non-citizens alike, in the U.S. Among the services Choicepoint provides to the government is access to a previously undisclosed and vaguely described exclusive data searching system. This system, in effect, gives law enforcement and intelligence agencies the ability to use private data broker to do something that they legally can’t, keep tabs on nearly every American citizen and foreigner in the United States.” Does this concern you?
WILLIAM ARKIN: What do you think? Of course, it concerns me. I mean, I think that this is just one tiny picture of the actual amount of information which is collected by the F.B.I. and the intelligence community. We know that there are dozens of these databases, Cornerstone, TALON, [inaudible], the Coast Guard ICC database, the F.B.I. Guardian database, the F.B.I. TRRS database, the Joint Intelligence Task Force Counterterrorism Homeland Defense database, the SSOMB database, the BTS summary, the C.I.A. TD database, the NSA traffic database called Criss-Cross. I mean, we know that these databases are out there and that they all deal with domestic issues.
What is particularly worrisome right now is that the National Counterterrorism Center, which was set up as part of the Office of the Director of National Intelligence, is now working to conglomerate all of these databases and that the Counterintelligence Field Activities, CIFA of the Department of Defense, is working to ensure that the military gains access to all of these databases, as well. So each of these, which goes into the creation of various watch lists and various tip-offs for the military or the intelligence community to surveil certain people, that determine the key words that the NSA or the F.B.I. then uses in its surveillance to catch certain emails or certain telephone conversations or certain international communications, all of these are now becoming more and more efficiently employed, the notion being that somehow we’re going to catch the next Mohammed Atta, but the reality being that huge numbers of innocent, non-threatening American citizens are being sweeped up in this gigantic swirl.
JUAN GONZALEZ: But what’s been the role or what should be the role of Congress in all of this, given the fact that at least you would think the libertarian trend within the conservative Republican movement would be aghast at this development, this continuing development of this enormous surveillance operation?
WILLIAM ARKIN: Well, my guess will be that Congress will gingerly handle this matter. There was some complaint issued yesterday by Bill Nelson of Florida in response to the Lake Worth surveillance. Other usual suspects will speak out, but, you know, look, as long as we pledge allegiance to 9/11, it’s going to be pretty tough for Congress people to question the validity of the notion that the United States is just another battlefield in the war on terrorism. And that is the sort of premise that we operate under, which provides both the threat picture and the mission responsibility for the military and the intelligence community to undertake activities in the United States in fighting the war on terrorism. No one wants to be responsible for missing the next dot that could be connected to the other dots.
So, I think that what we’re seeing in this debate about domestic spying that has sort of come out of nowhere in the last couple of weeks, and what we’re seeing in John Murtha’s breaking ranks with the administration on Iraq and the 9/11 Commission’s continuing work itself, is, I think, the beginning of a questioning of some of the very fundamental premises behind the war on terrorism, and until we are able to have that debate, I find it unlikely that the Pentagon’s review of this matter is going to result in anything beyond some wrist-slapping and some promises that they’ll tweak the rules.
AMY GOODMAN: Bill Arkin, we want to thank you for joining us and for getting these Pentagon documents, this database of about 400 pages that show scores of anti-war groups, particularly anti-recruiting groups, being monitored by the Pentagon around the country.










Media Options