
We speak with Jeremy Scahill of The Intercept, which has obtained a secret, internal U.S. government catalog of dozens of cellphone surveillance devices used by the military and by intelligence agencies that offers rare insight into the spying capabilities of federal law enforcement and local police across the country. The catalog includes details on the Stingray, a well-known brand of surveillance gear, and other devices, some of which have never been described in public before. Scahill says the catalog represents a trove of details on surveillance devices developed for military and intelligence purposes but increasingly used by law enforcement agencies to spy on people and convict them of crimes.
Transcript
JUAN GONZÁLEZ: Jeremy, I wanted to turn to another article that you had written recently on the new surveillance gadgets—
JEREMY SCAHILL: Yeah.
JUAN GONZÁLEZ: —that have been developed by our government that people aren’t aware of.
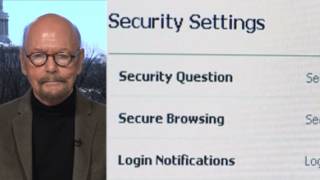
JEREMY SCAHILL: Right, the Stingray technology. Well, I mean, Stingrays have been around since the 1990s. And basically, you know, when cellphones started to emerge and then it became clear that that was going to be a very serious technology that was widely used, the FBI and other domestic law enforcement agencies started to become concerned about how they would be able to monitor people’s communications. And in the beginning, it was fairly easy for them to do this, because they were using radio waves. And, in fact, there was a famous case in which a retired couple in Florida, that were sort of amateur radio operators, were able to pick up phone calls of then-House Speaker Newt Gingrich. And that’s really how this kind of came to light in the U.S. Congress that, you know, there was a vulnerability in cellphones. But for the FBI and other agencies, the vulnerability was a good thing. I mean, now we’re looking at this whole issue about the iPhone and unlocking it in San Bernardino. I mean, that’s just the very current, modern iteration of the challenges that U.S. law enforcement was facing with trying to access these communications.
And so, what was created for a military purpose—and this often is what happens. This is what we see with the militarization of law enforcement in the U.S. The surveillance platforms that were created by and for the NSA, the CIA, other intelligence agencies, the U.S. military to target the communications of terrorists or adversaries or, you know, drug syndicates, smugglers and others started to become a common part of police in this country, both on a local and state level, and also the FBI, on a federal level, for using these devices to target people in routine criminal investigations. And, you know, there are—Stingray is sort of like Kleenex. Kleenex is actually a brand. You know, it’s like facial tissue is the actual thing. Stingray has now just become a term that is used to describe any of these devices that can essentially break down the security of mobile devices and access data.
And, you know, the ACLU has filed many, many lawsuits and FOIA requests around the country. And, I mean, the number of agencies in the U.S. that are using these kinds of devices is extraordinary. I mean, there’s almost no major law enforcement entity in the U.S. that isn’t using some form of a Stingray. And it’s a very invasive technology that is not very discerning, meaning you can get the, quote-unquote, “bad guys’” communications, but you’re going to get a whole lot of other people’s data, as well. And that’s the civil liberties argument with this. But there is a race between, you know, users of this—of cellphones and computer technologies, and law enforcement and intelligence agencies to try to break down that privacy.
And in some ways, you know, the battle that’s happening between the White House and the FBI and Apple is a little bit of theater of the absurd. And when you talk to people that are really seriously in the business of monitoring the communications of terror cells and others, the NSA is way ahead of everyone in this. And the idea that Apple somehow is providing terrorists with something that they can’t crack into is just false. And the backdoor thing—you know, serious people that work in hacking on behalf of the U.S. government, they laugh at the idea that a backdoor would solve their problems. They can hack people’s phones. They can hack through the encryption of many of these platforms. So, in a lot of ways, this is—they’re using terrorism as a way to try to ensure that, when necessary, they can immediately access data on anyone’s device in this country or around the world.
AMY GOODMAN: We’re going to break, and then, when we come back, I want to ask Matthew Cole about the Navy SEAL who turned over the photograph of bin Laden’s body, who is under investigation for his business ties. And we want to try to get to the whole issue of drone strikes, most recently in Yemen and Somalis. Jeremy Scahill, co-founder of The Intercept, and Matthew Cole, national security reporter for The Intercept, are our guests for the hour. Stay with us.
[break]
AMY GOODMAN: “Romero” by Julie Rickman. Archbishop Óscar Romero was assassinated 36 years ago, March 24th, murdered by members of a U.S.-backed death squad while delivering mass in San Salvador, El Salvador.









Media Options