
Topics
Guests
- Ronald Deibertdirector of the Citizen Lab at the Munk School of Global Affairs, University of Toronto.
Part 2 of our conversation with Ronald Deibert, director of the Citizen Lab at the University of Toronto. Citizen Lab recently revealed how the Mexican government used Israeli-made spy software to surveil a team of international investigators who had dispatched to Mexico to investigate the high-profile disappearance of 43 students at the Ayotzinapa teachers’ college in Guerrero in 2014. Deibert talks in depth about how Mexico, Russia and the United Arab Emirates have used cyberwarfare techniques to target civil society.
Transcript
AMY GOODMAN: This is Democracy Now!, democracynow.org, The War and Peace Report. I’m Amy Goodman, as we continue to look at how the Mexican government used Israeli-made spy software to surveil a team of international investigators who had been dispatched to Mexico to investigate the high-profile disappearance of 43 students at the Ayotzinapa teachers’ college in Guerrero in 2014. The targeted individuals included some of Latin America’s most prominent lawyers, who had been granted a form of diplomatic immunity to carry out their investigation. The spying was exposed by the Citizen Lab out of the University of Toronto.
Still with us is Ron Deibert, who is director of the Citizen Lab.
In Part 1 of our conversation, Ron, we talked about this spyware, Pegasus, and how it was deployed onto the phones or—what?—I think you call it “infecting” the phones of the globally respected investigators who investigated the disappearance of—this very high-profile disappearance of 43 students. How did you track this down? How did you know that this was being used? And how did the people on the ground understand that they were being spied on, that their phones had actually become, whether they’re on or off, a kind of megaphone both recording and projecting their voices and video to the government or whomever?
RONALD DEIBERT: Yeah, so, it’s a great story, Amy, but first let me underline that, as far as we know, none of the targets clicked on the link. Had they clicked on the link, then their phones would have been infected with Pegasus spyware, allowing the operators to take control. What we are able to say definitively is that they were targeted. It’s an important distinction. We examined the messages they received, and we could see clearly that this is an attempt to get them to click on a link, which would have then infected their phones.
AMY GOODMAN: Let me—
RONALD DEIBERT: How this all—
AMY GOODMAN: Let me just say something.
RONALD DEIBERT: Yeah.
AMY GOODMAN: If someone is to get that, how does it come? As a text? As an email? And how do you know not to do it?
RONALD DEIBERT: You might not necessarily know how to do it. In fact, part of the interesting aspect of the research that we’ve done here is the degree to which whoever was behind this took really quite extreme steps to try to trick people into clicking on the link. So, the international investigators received SMS messages, text messages, that contained content about supposedly someone’s father’s funeral: “Here are the details about my father’s funeral. He’s passed away. I thought you might want to come. Click on the link for details.” In the other previous cases that we looked at, there are far more egregious examples, things like: “There is a white van outside your house. Here is a picture of the people that are stalking you,” ” Here is a report that contains allegations about you that’s about to air on the television tomorrow. Click on the link.”
Probably the worst that we saw, however, was the targeting of a minor child of one of the journalists, Carmen Aristegui. Her son Emilio, a minor child attending school in the United States, received numerous text messages from the operators, presumably to try to infect his phone and then collaterally get at his mother, or perhaps something more sinister. Those messages he received including—included fake communications from the U.S. Embassy saying that there are problems with his visa, “Click on this link.” I’m not a lawyer, but as far as I know, that’s definitely a violation of diplomatic norms. It’s certainly possible that it’s a violation of a U.S. federal criminal statute about impersonating U.S. government communications. And had he clicked on that link and his phone been surveilled, that would have definitely been a violation of the U.S. criminal code.
So what happens here is, targets are sent inflammatory, emotionally charged messages, scary messages, maybe in rapid succession, in the hope that someone will click on that link, and it will infect their phone.
You asked earlier how we knew about this at Citizen Lab. The story actually goes back to August 2016, about a year ago, when a human rights defender, Ahmed Mansoor, in the United Arab Emirates, received very similar suspicious messages on his iPhone. And we had done several reports with Ahmed going back a couple of years. He knew right away to be suspicious of them. The message—messages purported to show evidence of torture in UAE prisons, something, as a human rights defender, he might be tempted to look at. Instead, he forwarded those messages to us at Citizen Lab, and we did a forensic investigation of—by clicking on those links in a controlled environment. And that’s how we first came across the infrastructure of the NSO Group.
At that time, the infrastructure included very, very rare and precious unknown vulnerabilities into the iPhone. Apple products are very secure. You know, this type of vulnerability can cost millions of dollars. So we had to disclose the knowledge of that to Apple, and they issued a patch to all iPhone products worldwide, more than a billion users, last year.
But looking at those SMS messages, some civil society groups in Mexico thought, “Hmmm, maybe there’s targeting going on here in Mexico.” We had some evidence that there was at least one target in Mexico, when we examined some of the infrastructure. So our partners in Mexico—R3D, SocialTIC, Article 19—started doing outreach with lawyers, human rights activists and journalists, asking them to go back, examine their phones, see if they received any suspicious SMS messages. They were forwarded to us for analysis, and we were able to start determining who was targeted by this technology.
AMY GOODMAN: I wanted to read from #Technology News of Reuters. It says, ”NSO Group Ltd, a company that helps governments spy on mobile phones and is so secretive that it regularly changes its name, is exploring a sale that could value it at close to $1 billion, including debt, according to people familiar with the matter. The move comes as governments around the world, including the United States and China, increase spending on cyber security and warfare, boosting the valuation of technology companies that are active in the sector.” So explain more about what NSO did. Take off from where we talked about this in Part 1, what NSO is, Francisco Partners, and how governments with it around the world.
RONALD DEIBERT: Well, you’re absolutely right. This is part of a burgeoning cybersecurity marketplace. Cybersecurity is, you know, probably the biggest issue on the agenda for most governments around the world. There are very serious issues around data breaches, investigations into terrorism, national security investigations, all of which today requires this type of technology. So the marketplace is absolutely exploding.
The problem is that companies like NSO Group really face no outside scrutiny or serious controls of any sort in terms of to whom they sell the product. So, you know, most companies are concerned about the bottom line. They’ll take a client wherever they can. Some of them, like NSO Group, may claim that they undertake some kind of due diligence. In the case of NSO Group, they say, “We only sell to accredited government agencies, and we require them to only use it for national security or criminal investigations.” The problem, of course, is that many governments around the world today are corrupt or authoritarian or, if they’re democracies, they’re sliding back into autocracy. And for them, what constitutes a crime or a national security issue can end up being civil society. It can end up being investigative journalists, human rights advocates and even, in the case of Mexico, health scientists who are advocating for a tax on sugary beverages.
So, this is a marketplace that’s really out of control. And I think that unless there’s some kind of concerted effort that’s taken by the private sector, by civil society, by governments to control it, we will end up seeing much more of this type of abuse.
AMY GOODMAN: So, let’s talk about the case of the United Arab Emirates and how a dissident ended up in jail in solitary confinement.
RONALD DEIBERT: So, Ahmed Mansoor is the person I mentioned before. He has actually been the subject of three separate reports of ours, going back at least four years, where he has—his phone and his devices have been targeted by his own government, using products of three different companies: NSO Group, the most recent; prior to that, a company called FinFisher, which is a U.K.-based company that sells this type of spyware; and Hacking Team, which is an Italian company.
Thankfully, Ahmed is savvy enough to know not to click on suspicious links or open attachments. But many people might not be. It’s very tempting when you receive a message that looks alarming or maybe has salacious material or something that might interest you. Think of yourself, as a journalist, how often you click on links and attachments as you go about your daily routine. These companies exploit that interaction of trust that happens, and use their technology to get inside devices, typically by exploiting some problem with the software in the device that the manufacturers don’t know about.
Ahmed, unfortunately, after our report came out, was arrested by UAE authorities. He remains in jail. I’m not sure where the case stands right now. The last I heard, he was just being detained without any communication outside except to his lawyers and immediate family.
AMY GOODMAN: I’m looking at an Amnesty report that came out, I believe it was, in May, that says the—it was headlined “The Guy Who Saved Your iPhone from Hackers Is Stuck in a UAE Jail.” And it says, “The spyware which Mansoor had been targeted with was so sophisticated and expensive that Citizen Lab researchers dubbed him the 'million dollar dissident.'”
RONALD DEIBERT: Yeah. Yeah, that’s right. If you recall the controversy between the FBI and Apple over the San Bernardino iPhone, FBI was pressuring Apple to put in place some mechanism for them to be able to open up this device. Eventually they went to the private sector, because of Apple’s reticence to cooperate. And they reportedly paid more than a million dollars for the service to effectively break that iPhone. So that gives you some indication of how valuable that type of unpatched vulnerability is for something like an iPhone. It’s among the most secure products on the marketplace. Knowledge of vulnerabilities connected to those type of devices is a rare and precious commodity.
And law enforcement agencies, intelligence agencies increasingly want to get into people’s devices. First of all, we carry them with us wherever we go, so they’re very convenient ways to track targets. But also, many of us are now using end-to-end encryption. We’re encrypting our communications over email or chat messages, which means that intercepting communications traffic as it flows through networks is increasingly challenging and even, in fact, useless for analysts operating for governments. So, instead, they want to get inside the device. And once they’re inside the device, they can see everything that a person is doing, even read encrypted messages and emails.
AMY GOODMAN: I want to ask you about David Satter, among his books, his most recent, The Less You Know, the Better You Sleep: Russia’s Road to Terror and Dictatorship Under Yeltsin and Putin. Tell us about who he is and how he fits into this story.
RONALD DEIBERT: So, David Satter is, as you say, an investigative journalist who’s worked for many years on the Russia file. He was expelled from Russia for his reporting about corruption in the Russian government. And he shared with us an experience where he clicked on what he thought was a Google security warning, which ended up being an attempt by someone to get inside his email. They were successful. They fooled him. He entered in his credentials mistakenly. And they sucked up all of his emails. And then, a few weeks later, portions of those emails, as well as documents contained in his emails, appeared on a Russian-affiliated leak website. However, they were tainted. Disinformation was put in some of the documents to make it appear as if Satter was part of a CIA-backed operation to subvert the Putin regime. They associated him with Alex Navalny, for example, even though he was not paying Alex Navalny, a prominent Russian activist.
When we examined the technical details of this particular espionage campaign against David Satter, we were able to unravel more than 200 other targets, people who were targeted by the same operators behind this campaign. We were also able to associate some of the technical indicators with the very same espionage campaign that got inside Podesta’s email and the DNC. So, even though we can’t show definitively that this is a particular agency or an individual within the Russian government, it’s clear that this is the same group. Russian-sponsored espionage operators who targeted the American election were here targeting journalists, human rights activists and civil society groups.
AMY GOODMAN: Ron Deibert, director of Citizen Lab, we’re speaking to him in Toronto. He is at the University of Toronto. You wrote a piece in January, “The DHS/FBI Report on Russian Hacking was a Predictable Failure.” You mean the Department of Homeland Security/FBI report on Russian hacking, a predictable failure. Explain.
RONALD DEIBERT: Well, I think many people, myself included, were really hoping that there would be some kind of definitive evidence coming out of the intelligence community about the Russian involvement in the espionage against the DNC. At the same time, I wasn’t holding my breath, because there are structural factors that really prevent agencies like that from disclosing all of what they know. And if you recall, the report that came out from the DHS was widely criticized, by myself and others, lacking technical details, having contradictory information, really short—having shortcomings in many respects. And you would expect that. Intelligence agencies don’t like to disclose things to the public. They don’t like to disclose means and methods.
Meanwhile, cyberespionage is something that increasingly affects us all. As we’ve shown at Citizen Lab in our research, there’s really, I would call it, an epidemic of targeted digital espionage against civil society worldwide, against journalists, human rights advocates and so on. And yet we have very little evidence that comes into the public domain about this, because it’s either withheld by governments or it’s, you know, something that the private sector does, but, for them, civil society is not a profitable client. So we have a kind of market failure here when it comes to investigations and evidence around targeted digital attacks against civil society. I think we need to rectify that. We need to change that by having many more groups like Citizen Lab out there. I believe there’s no reason why other university-based groups couldn’t be doing the same type of evidence-based research into cyberespionage that we’ve been successfully doing for the last 10 years.
AMY GOODMAN: Ron Deibert, what does the U.S. government, FBI, local law enforcement use inside the United States? Are they using Pegasus itself? Or what similar technology is used?
RONALD DEIBERT: They could be. It really is, I think, you know, first and foremost, that the techniques, the tradecraft around surveillance over the last decade has really amplified. And it’s happening at the same time that we’re effectively turning our digital lives inside out. You know, most of us carry mobile devices. We’re constantly engaged online. And that means there’s a trail across the electronic ecosystem, many different opportunities for whoever wants to do monitoring to pick up trails of our communications. One method is to try to infect a device with malware. Certainly, agencies of the U.S. government use this type of malware—the NSA, the CIA. There are leaked—there’s leaked evidence of this on WikiLeaks, for example, the use of CIA malware. Law enforcement at local levels, whether they use it or not against U.S. citizens, I think that’s an interesting question for journalists and researchers to investigate. There are also tools that pick up cellphone signals, called IMSI-catchers or Stingrays. And, of course, in the United States, authorities have access to the infrastructure of the telecommunications companies. They’re able to, either through warrants or other means, ask them for user data directly. So there are a variety of methods that U.S. agencies can use to monitor a citizen’s communications.
AMY GOODMAN: Let me ask you what your take was on this Trump plan to have a cybersecurity unit working with Russia. I wanted to ask you about that and also what you feel journalists should be asking about the whole Russian cyberhacking scandal in the United States.
RONALD DEIBERT: Well, I really don’t even think that proposal for—what was it?—an impenetrable cybersecurity unit to guard the negative things—it’s so ludicrous, it’s not even worth commenting on. We have mountains of evidence, that are accumulating, that show collusion between the Trump administration and the Russian government. I, for one, have read extensively about Russian cyberespionage. You mentioned our “Tainted Leaks” report. I encourage people to google that report and look carefully at the details there. There’s no doubt in my mind that actors affiliated with the Russian government tried to influence the U.S. election process. They are the ones that were responsible for breaching the computer systems of the DNC, John Podesta’s emails, as well as many other groups that we identified in our report, groups and individuals.
AMY GOODMAN: Why are you so convinced of this, Ron?
RONALD DEIBERT: Well, first of all, there are technical indicators—it would take a while to go in to explain this—you know, the methods, addresses, domains, techniques and tradecraft that are used by groups repeatedly, that target specific categories of individuals that are of interest to the Russian government and that have been doing this for a long period of time. So, you know, there’s a community of security researchers, some in the private sector, some like us, some in government, that all converge on the same conclusion, that these groups are affiliated with Russia.
The reason that people have difficulty saying, “Oh, it’s definitely Russia,” is because of the way Russia operates cyberespionage. Typically, they outsource it to proxy groups, to criminal actors. Of course, crime and corruption run throughout the Russian system itself, including the FSB and the security services. So it’s very common for them to work with organized criminal groups to do this sort of campaigning. One minute, these groups might be engaged in some kind of cyber crime for fraud, theft of credit cards, whatever. The next minute, they’re targeting the oil and gas sector. The next, they’re targeting journalists like Satter, and on and on. So there’s no doubt in my mind that this has been going on.
AMY GOODMAN: And does the U.S. do this?
RONALD DEIBERT: Of course they do. They do it in a different way, though. They have a long history of engaging in surveillance and interference in domestic elections throughout the world. That’s, you know, on the public record. They tend not to use proxy actors or criminal groups in the same way. They have better in-house capabilities, frankly, and a far wider global reach in terms of being able to access parts of the telecommunications infrastructure that is owned by U.S.-based companies. So it’s a different modus operandi, but, certainly, the United States is able and does do this type of surveillance routinely.
AMY GOODMAN: And—
RONALD DEIBERT: I would say there’s one key difference, of course, is that the checks and balances, however flawed they may be, in the United States are far more rigorous than just about any other country on Earth, and certainly far, far greater than Russia, which is a kleptocratic regime. We have, essentially, an autocrat, and there’s corruption throughout the government—no meaningful checks and balances around how that’s deployed. It would be far more difficult for U.S. agencies to engage in abuse of that type of surveillance, given the checks and balances that exist in the United States.
AMY GOODMAN: You not only talked about Russian cyberhacking, but you said there’s no question that they colluded with the Trump campaign. Explain what—that part of the evidence.
RONALD DEIBERT: Well, I’m just looking at the public reporting that everybody else is. And what more do you need than the emails that were released yesterday that show definitively that there was collusion going on?
AMY GOODMAN: So, let me ask you, then, overall—I have a piece here from The New York Times that says, “Want to invisibly spy on 10 iPhone owners without their knowledge? Gather their every keystroke, sound, message and location? That will cost you $650,000, plus a $500,000 setup fee with an Israeli outfit called the NSO Group. You can spy on more people if you would like—just check out the company’s price list.” So, talk about, then, how that works, who the players are that are using it, even though you say the NSO Group says they just give it to governments, that anyone, if the price is right, will use it. And then, does the NSO, like in the case of Mexico—do they then gather the information, as well? And what role does the Israeli government play in this?
RONALD DEIBERT: So I think the way to think about this is there’s a wide spectrum here. So, on one end of the spectrum, you have agencies like the United States National Security Agency, that has very powerful in-house capabilities, billions of dollars they devote to developing tradecraft and techniques in-house. Then you have the commercial marketplace. So, for those governments who don’t have the type of capabilities in-house, they can go to companies like NSO Group and others and simply purchase their own NSA, if you will. And, of course, many governments have both the dollars to do that and the appetite to do it, as well.
And then, at the far end of the spectrum, you have low-end kind of cybercriminal techniques that are just as useful as some of the multimillion-dollar surveillance technologies, simply because they work. If you can get someone to click on a link containing malicious software, and considering that many of us use unpatched software or old, outdated software or don’t even know how to update our—the software that we use, those techniques can be just as effective. And we see them throughout the world. In fact, if you look at how Russian-affiliated operators were able to hack into the DNC and so on, really, there was no sophistication there. They simply tricked people into entering in their credentials into what like—into what look like Google security warnings.
In terms of whether these companies collect the same information or know about how their products are being used, that’s a really good question, because it speaks to the issue, really, of know thy customer. These companies have an incentive to simply wash their hands of it and say, “We sell it, but we don’t know how it’s used.” Of course, that’s simply not true. The companies may not know exactly how their clients are going to end up using them, who they’re targeting, but they can certainly see how the infrastructure is being used, and take measures to prevent abuse from happening, after the fact. If we can, at Citizen Lab, analyze all of this and discover it, certainly so can companies that purport to be advanced surveillance technology companies.
Your question about Israel is very important, as well. NSO is an Israeli-based company. It’s up to citizens of Israel to decide whether companies operating in their jurisdiction should be able to willy-nilly sell this type of technology to autocrats and dictators. I hope that this will open some eyes in Israel and encourage or motivate Israeli lawmakers to strengthen export controls, because export controls, although not perfect, are one mechanism to control the abuse of commercial spyware.
AMY GOODMAN: Is there any evidence that they’ve used it?
RONALD DEIBERT: That who has used it? Sorry?
AMY GOODMAN: Israel has used it, that the Israeli government has access to it?
RONALD DEIBERT: Well, not this particular case, but, bear in mind, Israel is a very advanced country when it comes to digital surveillance. They have their own NSA, called Unit 8200. And, in fact, it’s unique insofar as it’s a very entrepreneurial-minded agency. So, veterans of Unit 8200 are encouraged to go out and build startup companies. That’s precisely why you see most of the best facial recognition, surveillance companies, companies that engage in deep packet inspection of massive internet traffic tend to be Israeli companies. They’re very good at it, and they’re encouraged to build startups.
AMY GOODMAN: And did you say whether the NSO has all this information, that all these governments are gathering, if they’re using Pegasus?
RONALD DEIBERT: I doubt they would have everything. It really depends on how the—how the service is set up and how the technology is deployed. I doubt that they would, you know, want to put themselves in a position of liability even of collecting all of that. But they know when their infrastructure is being used. And that means when targeting is happening, when domains are being accessed. We know that, in fact, because after our reports came out, they shut down some of the domains that are associated with the text messages that we’ve been documenting. So they’re certainly aware of when their product is being used. Some of the companies in this sector go further and offer various forms of technical support, helping to craft, for example, the phishing emails or the phishing messages that are used to target individuals.
AMY GOODMAN: And when you say “phishing,” for laypeople, that P-H-I-S-H, explain.
RONALD DEIBERT: Think about it as an attempt to trick you and deceive you into clicking on a link or opening an attachment, in the way I described before.
AMY GOODMAN: You mentioned in Part 1 of the conversation that you started this work around food scientists in Mexico. Can you elaborate on that? You were using it to just preface the whole discussion of spying on the investigators of the 43 disappeared students, but tell us more about that first story.
RONALD DEIBERT: Well, if you recall, when we did our report in August 2016 concerning Ahmed Mansoor in the United Arab [Emirates], we had some technical indicators that showed that there was some targeting going on in Mexico. We had searched all of Twitter, looking for links that might have been sent out on Twitter, and discovered there were a few that were Mexican-themed. And we knew of at least one target in Mexico, a journalist. We have partners in civil society—in this case, local Mexican NGOs: R3D, SocialTIC, Article 19. They were certainly aware of our research and had their radar up for any reports that may come to them. There’s another advocacy group called AccessNow that operates a digital help line, and they received reports about—from people saying, “Hey, I think I received some kind of suspicious text message. It looks like what I read about in The New York Times that the Citizen Lab reported on.” So, working with our Mexican partners, we did outreach. They contacted groups that made these type of claims. We gathered, with their cooperation, the evidence of the SMS messages and compared it against the technical indicators that we’ve had. And actually it’s been a very fruitful partnership, because one case has led to another. We’ve done four separate cases now in Mexico, 19 individuals targeted now in total. I suspect that the number will increase as we start hearing more about other targets.
AMY GOODMAN: Finally, Ron Deibert, we’re speaking to you on a day of global protest around keeping the internet open and free. And you’re talking about governments increasingly using, and corporations increasingly getting involved with, spying and, you know, top-secret use of this spy cybertechnology. Can you talk about, on the one hand, the attempts of governments to close down the internet, to use cyberspying on people and, you know, what this means today, the—how concentration of power, used in all sorts of cyber ways, is increasing inequality in access to information?
RONALD DEIBERT: Well, I think the way to think about it is, we’ve developed this wonderful technology that is actually, I believe, essential to the future of the human species. We need to be able to communicate with each other, access information, if we’re going to manage the planet, solve our problems together collectively. If you look back 20 years ago, most governments really didn’t care about the internet. They didn’t have internet policies, digital policies. Fast-forward to today, cybersecurity is at the top of the agenda. Almost every government has cybersecurity policies. They have agencies that are devoted to, if not cyberwarfare, certainly cybersurveillance. Digital surveillance is rampant. There’s a huge, multibillion-dollar marketplace that puts in the hands of policymakers capabilities they never before imagined to engage in the type of attacks that we’re talking about and much more. So, what was once a kind of global commons of information is quickly being carved up. It’s become an object of intense geopolitical contestation, to the point where I feel, much like the natural environment, the global environment, there’s significant degradation of the global communications environment.
So we have to start thinking broadly as citizens of this planet how we tend to, how we engage in stewardship over cyberspace collectively. That means thinking about ways to control the abuse of spyware, thinking about applying techniques of arms control to this domain, and, ultimately, reinforcing checks and balances around intelligence agencies, law enforcement and so on, around the use of these advanced technologies to engage in surveillance. Unfortunately, it’s an uphill battle, and it’s getting steeper. Most governments are democratically challenged. Unfortunately, even your own government is going through a horrible episode in this respect. So, we’ve got a long road ahead of us. But that’s my vision, anyway.
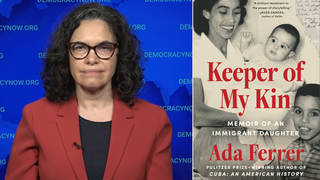
AMY GOODMAN: Well, Ronald Deibert, I want to thank you for being with us, director of the Citizen Lab at Munk School of Global Affairs at the University of Toronto. Thanks so much for joining us.
RONALD DEIBERT: My pleasure, Amy. Thank you.
AMY GOODMAN: This is Democracy Now!, democracynow.org, The War and Peace Report. To see Part 1 of our conversation, you can go to democracynow.org. Thanks so much for joining us.












Media Options