
Guests
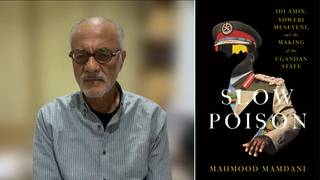
- Ronald Deibertdirector of the Citizen Lab at the University of Toronto and author of Reset: Reclaiming the Internet for Civil Society.
In Part 2 of our interview with Ronald Deibert, director of the University of Toronto’s Citizen Lab, he describes how they discovered a massive security flaw that was being exploited by the Israeli-based NSO Group to infect Apple iPhones and other devices with its Pegasus spyware. Deibert also describes how people can try to protect their devices from such security exploits, and the push to halt sales of this type of spyware. Deibert is the author of “Reset: Reclaiming the Internet for Civil Society.”
Transcript
AMY GOODMAN: This is Democracy Now!, democracynow.org, The War and Peace Report. I’m Amy Goodman, as we bring you Part 2 of our conversation about this epic Apple correction that has been made. Apple has released an emergency software update to fix a security flaw in its iPhones and other products researchers found was being exploited by the Israeli-based NSO Group to infect the devices with its Pegasus spyware. Over 1.65 billion Apple products in use around the globe were vulnerable to the spyware since at least March. Apple said vulnerable devices could be hacked by receiving a malicious PDF file that users didn’t even have to click. It’s known as a “zero-click” exploit.
The flaw was discovered by the University of Toronto’s Citizen Lab, which found the hack in the iPhone records of a Saudi political activist. Earlier this year, a massive data leak revealed Pegasus software had targeted the phones of thousands of journalists, activists and political figures around the world for foreign governments and NSO Group clients.
So, we’re continuing our conversation now with Ronald Deibert. He is the director of the Citizen Lab at the University of Toronto. His book is called Reset: Reclaiming the Internet for Civil Society.
So, let’s continue, Ron. If you could talk about, first of all, what this “zero-click” exploit is, for laypeople who can’t even understand that, but how so many phones, iPhones, iPads, got infected, and how people can protect themselves?
RONALD DEIBERT: Sure. Thank you, Amy. Well, let me answer the last question first. There really is nothing that a person alone can do to protect themselves against this, other than update their software, unfortunately. This is highly sophisticated surveillance technology. So, basically, all of us carry around with us all the time these little devices, which are very handy. An Apple product, generally speaking, is very well engineered. They pride themselves on their security, which goes to show how sophisticated this technology is.
So, a company like NSO Group hires the most well-trained surveillance engineers. In the company’s case, they come from Israel’s signals intelligence agency. Most of them are graduates from Unit 8200. And they spend their entire day scouring these applications, that are contained on devices like iPhones, looking for a little flaw that the engineers didn’t anticipate or design in a way that could be exploited by the company.
And what they want to do is move, ultimately, to the point — which they have accomplished now — to require no interaction on the part of the target. So, all of us now have become familiar with things like attachments that come to you unsolicited, or maybe a text message with a link. In the past, surveillance companies relied on that type of exploit. It would require you to be effectively tricked into doing something, through some kind of social engineering. This surveillance iteration, the latest iteration, simply could be sent at a device and silently commandeer it.
What does that mean? Well, once this happens, a target can be monitored as — from an operator remotely, as if they were inside that device. That is, effectively, having a spy in your pocket. They could read every email, every text message. They could, of course, track your location through the device’s GPS system. They could turn on the video and audio mechanisms to capture the surroundings, the audio of a room that you’re in, effectively intercept any type of conversation.
So this is very powerful technology, which is why this marketplace is exploding. It’s very lucrative for companies like NSO Group. But there is, as it stands now, absolutely no regulation over this marketplace. We’re seeing the proliferation of this technology globally, with nothing to mitigate the type of harms we, at the Citizen Lab, and others have documented.
AMY GOODMAN: And so, now talk about this no-click exploit, and your alerting Apple to this, and what has to be done now.
RONALD DEIBERT: Well, you know, thankfully, Apple took this very seriously. We are grateful that they are receptive to having security researchers share with them this this type of data, because they could move very quickly to patch and update the software of 1.65 billion users. That’s what we want tech platforms to do. They have a responsibility to take care of problems like this when they’re identified, which means it’s very important for them to be open to security researchers, even ones like us at the Citizen Lab. You mentioned I wrote this book Reset. I’m very critical of most of the tech platforms, including, for various reasons, Apple. We are at arm’s length from Apple. We’re an adversary of the company, if you will, which means it’s very important that those companies put that stuff aside and be open to receiving data and working with security researchers to effectively improve the security of everyone.
But underlying this is a more serious problem. We live in a digital ecosystem where the philosophy basically is to move fast and break things. So that means applications and variations of applications are being pushed out relentlessly to us. Those need to be engineered better. The companies need to step up. And messaging applications have become really an irresistible soft target.
So, this zero-click spyware involves no interaction with the user. NSO Group simply pushes code out to a device and takes it over without a user noticing anything. That’s like a nuclear bomb of surveillance technology, if you will.
AMY GOODMAN: And talk more about the NSO Group, exactly who they are made up of, who they are working for.
RONALD DEIBERT: Well, NSO Group is merely one among many mercenary spyware companies that exist globally. It happens to be one that is notorious, frankly, because we and others have documented the abuse of its surveillance technology, because we work with civil society. And we have, at the Citizen Lab, a dedicated research program, where we enroll human subjects in a study that we infer or hypothesize are likely targets, and we investigate their phones. But it’s not the only company in the world.
This one is interesting in a variety of ways. It’s a company that is very lucrative, valued at well over a billion dollars, was about to go public. I’m not sure if they still will, after the Pegasus project and these latest revelations. It’s made up of engineers who come from Israel’s very sophisticated signals intelligence agency, for the most part. They’re graduates of that agency, Unit 8200. So, they are the most well trained at this sort of thing.
When you think about it, kind of stepping back historically, it’s really kind of curious that you have basically the capabilities of one of the world’s most sophisticated nation-state espionage operators being turned into a commercial product. So, that means governments that lack those capabilities but have deep pockets can simply go and purchase this type of despotism as a service off the shelf. We’ve never seen anything like that historically, the privatization of this type of digital espionage. There is no regulation over this marketplace. It’s stunning, actually, to see, you know, a lengthy list of abuses — not surprising, but still very stunning.
AMY GOODMAN: So, can you talk about the Saudi activist, where you discovered the flaw?
RONALD DEIBERT: Well, as you know, Amy, we are based at the University of Toronto, and we approach this topic as academic researchers. And anyone who participates in a research project that we run is guaranteed confidentiality. And that includes this particular Saudi activist. So we can’t say much about this person, other than to say, sadly, that the Saudi regime is notorious for this type of abuse of surveillance technology. Recall that the murdered Washington Post journalist Jamal Khashoggi, we and others determined that his inner circle had their phones hacked with NSO Pegasus, and we attributed that to the Saudi government, with a high degree of confidence.
So this is a serial abuser of surveillance technology and a regime that has used this type of surveillance technology to identify, neutralize and murder its critics. So, I hope that that puts into perspective the reality of what we’re dealing with here, the very dark reality of this type of technology. It’s no joke.
AMY GOODMAN: You know, last July — that’s July 2020 — a Moroccan court sentenced the independent journalist Omar Radi — Omar Radi is someone that we interviewed on Democracy Now! They sentenced him to six years in prison, arrested last year on what press freedom advocates call retaliatory charges. For years he’s been targeted by Morocco for his reporting on corruption and human rights. Last year, Amnesty International revealed Moroccan authorities had hacked his phone using Pegasus spyware from the NSO Group. We spoke to him last year, just weeks before he was arrested. This is what he said.
OMAR RADI: Pegasus is a quite silent program. You don’t feel it, actually. And it’s not a persistent program. It doesn’t stay in your phone or in your computer. It works using a network injection, so people need to be near you to make themselves pass as a relay antenna. And your phone is connected to a fake relay antenna, and then the network injection works, and then the program works, and they get — I don’t know. It has a lot of features. It can use your microphone, it can use your keyboard, it can use your screen, and get any information that is stored in your phone.
So, I don’t know the amount of information they’ve stolen from my phone. But I’m sure, in this pro-medias — pro-state medias, they published many information that I have exchanged even in Signal, which is known that is a very safe program. So I have evidence that my own conversations have been leaked to pro-state media, the same that are leaking also my bank information.
AMY GOODMAN: So, that’s the Moroccan journalist Omar Radi. We did that interview over a year ago. Right afterwards, he was imprisoned, and he was sentenced to six years in prison. Ronald Deibert?
RONALD DEIBERT: Well, this is, sadly, a — it’s becoming a routine part of the world that I live in. As part of our research, we see many, many examples similar to this one. Literally, we have documented thousands of cases of journalists, activists, lawyers, human rights defenders, researchers, public interest advocates whose phones have been hacked by governments like Morocco, Saudi Arabia, United Arab Emirates, Mexico. A tsunami of abuses of this type of technology is the only way I can describe it.
Even family members of targets will have their phones targeted in this manner. Why? Because getting access to maybe your child’s device is a way to indirectly get access to what you’re communicating or who you’re communicating with. It’s a soft entry point, if you will. Nothing is out of bounds for the government clients of this type of surveillance technology. And so, not surprisingly, we are seeing, like I said, a tsunami of abuses of this sort.
AMY GOODMAN: Ron, I wanted to turn to NSA whistleblower Ed Snowden, who told The Guardian spyware sales need to be stopped. This is what he said.
EDWARD SNOWDEN: If you don’t do anything to stop the sale of this technology, it’s not just going to be 50,000 targets, it’s going to be 50 million targets, and it’s going happen much more quickly than any of us expect. The way we do it is to halt the trade around this technology.
AMY GOODMAN: So, that’s Ed Snowden.
RONALD DEIBERT: Right.
AMY GOODMAN: Ronald Deibert, again, you’re director of the Citizen Lab at the University of Toronto, author of the new book Reset. Can you talk about the hacking ability of the NSA — he was a NSA consultant, National Security Agency consultant — the role of former NSA contractors in selling their skills, that they learn at the NSA, to help these private spyware companies?
RONALD DEIBERT: Sure. Ed’s assessment is 100% accurate. Look, if you step back and kind of look at this historically, what we have seen is, as the digital ecosystem has basically surrounded us, as we’re immersed in these type of technologies, it’s not surprising that government intelligence agencies would devote extensive resources to being able to tap into and monitor and take advantage of all of this data circulating. That’s what they do. And, of course, many of them have huge budgets. You talk about the NSA. Think about their budget and the resources they can devote to this.
But we live in a world also defined by privatization. And so, most of these government agencies, especially ones like the NSA, and the same in my own country, here in Canada, will contract with private companies to supply them with products and services, basically providing them with hacking capabilities. Some of these companies are very sophisticated. They themselves come from — are made up of graduates of these intelligence agencies. You mentioned in your report earlier this indictment against three individuals from the Department of Justice. These were former engineers at the U.S. National Security Agency who, perhaps not surprisingly, went out and found employment at a startup that was being directed by the security agencies of the United Arab Emirates. What did they do? They went out and they targeted opposition figures, and even us at the Citizen Lab were apparently targeted by these groups.
So, think about that for a minute, the privatization of this type of spying capability at a time when so many governments lack proper oversight, basic controls over what those security agencies do, and are run by kleptocrats, dictators, autocrats, etc. That’s a very potent mix, dangerous equation for human rights right now.
AMY GOODMAN: So, Ron, we’ve talked about what the spyware — what information it can get from your phone or your device. But what about — can it put incriminating information into your iPhone or iPad or computer?
RONALD DEIBERT: Absolutely, absolutely. I mean, think of it this way. The operator who — let me say again — thanks to companies like NSO, can silently commandeer any device in the world, can do anything with that device, including putting incriminating information on it. We’ve seen cases like this, not using NSO’s spyware but a different type of surveillance technology, in India. So, this has been documented. It’s something that is a very real risk.
AMY GOODMAN: The NSO Group in August released a statement saying, in part — and let me quote this — “The report by Forbidden Stories” — that’s your group, Ron. “The report by Forbidden Stories is full of wrong assumptions and uncorroborated theories that raise serious doubts about the reliability and interests of the sources. It seems like the 'unidentified sources' have supplied information that has no factual basis and are far from reality. After checking their claims, we firmly deny the false allegations made in their report. Their sources have supplied them with information which has no factual basis, as evident by the lack of supporting documentation for many of their claims. In fact, these allegations are so outrageous and far from reality, that NSO is considering a defamation lawsuit. … We would like to emphasize that NSO sells its technologies solely to law enforcement and intelligence agencies of vetted governments for the sole purpose of saving lives through preventing crime and terror acts. NSO does not operate the system and has no visibility to the data.” Now, that’s NSO’s response to your investigation, University of Toronto’s Citizen Lab. Can you respond, Ronald Deibert?
RONALD DEIBERT: Sure. So, first, let me make a little clarification. We’re not Forbidden Stories. They’re partners of ours. That’s a consortium of journalists that we and others worked with, and Amnesty International worked with, on the latest Pegasus project stories. So, you know, this is — you know, as you read it out, I was thinking that this sounds like it was written by a lawyer and a public relations firm, which I assume it was.
NSO Group routinely comes up with these excuses. And usually they remark upon our reports with some kind of defamation of their own. They never — you know, we’ve produced dozens of reports. And, you know, we’re based at the University of Toronto. We’re not making this stuff up. This is research whose methods undergo extensive peer review. We are not, you know, conjuring up these things. These are not allegations. This is data. This is evidence. You know, you had Apple update their software on the basis of our investigation. Do you think they would be doing that if this was false? You know, we have published extensively on our website and other reports. The world has had years to look at this. Not a single error has been identified by the global scientific engineering community that can read our reports.
So, you know, it’s not surprising to me. Of course, they’re going to do — NSO Group, that is, and other companies like them — what they can do to continue to profit from this marketplace, because, Amy, it is very lucrative. And money attracts people, and, you know, they just want to continue with business as usual. And they will, unless something is done.
So, you know, look, the sand has run through the bottle here. We need to recognize that this is an issue that needs to be dealt with now. So governments have to do something about it; otherwise, we’ll see more of this. There will be a story tomorrow or next week on your program about another abuse of this sort. What do we do? That’s the question we should be asking here. And we really need to turn to governments to act now.
AMY GOODMAN: So, let’s end with that question. What can governments do? For example, in the United States, what legislation can be passed? And then, what can people personally do to protect their privacy?
RONALD DEIBERT: Well, there are a variety of things that could be done, from the very low-hanging fruit all the way up to quite extensive regulation. So, first and foremost, I think we need government leaders, you know, heads of state and others, to come out and speak publicly and say, “Yes, this is a very serious problem.” We were heartened to see the Department of Justice yesterday in those indictments actually describe the marketplace in basically the same language I’m using right now. They say this is a major privacy and security risk, this unregulated marketplace, and needs to be reined in.
First of all, most importantly, we need more transparency and accountability around this industry. That means that governments who are contracting with these companies need to exercise both export controls over them, but also more due diligence over what those companies do. They can do that if the United States, Canada, European countries, the U.K., France — who, by the way, heads of state, we know now, have been targeted using this technology. This is a national security risk for them. They need to get together and quickly regulate this marketplace. And if they did that, just with their own companies that they contract with, you know, push as part of the licensing agreements, as part of the purchasing requirements, some behavior rules around what those companies can do, make sure that they don’t sell to the Saudi Arabias of the world, etc., it wouldn’t take care of the entire problem, because we have companies coming from China, from other parts of the world, but it would at least mitigate some of the harms we are seeing.
Many people, my colleagues have talked about a moratorium. That’s how urgent this is. And I believe that Western liberal democracies who care about the rule of law and human rights and who are experiencing this type of targeting on their own soils, they need to do something like that right now. And hopefully, that would help solve some of the problems that we’re identifying, honestly, Amy, on a daily basis.
I mean, this is one report with an activist who chose to remain anonymous, which is an objectively rational decision for a Saudi activist to do, frankly. For every one of those reports, there are dozens of others that we’re constantly investigating, with companies other than NSO Group, as well. It’s not just one company, either. They get a lot of the attention, primarily because we’re exposing their operations continuously. But it’s a marketplace. It’s not one company. And it’s causing all of these external harms. So, the only way to solve this problem is by governments acting collectively to bring some order to what is now a Wild West marketplace.
AMY GOODMAN: Ronald Deibert, we want to thank you so much for being with us, director of the Citizen Lab at the University of Toronto, author of the book Reset: Reclaiming the Internet for Civil Society. Thank you so much for being with us.
RONALD DEIBERT: Thank you.
AMY GOODMAN: To see Part 1 of our conversation, go to democracynow.org. I’m Amy Goodman. Thanks so much for joining us.







Media Options